Enhancing REST API Security with JWT: A Practical Guide
Introduction
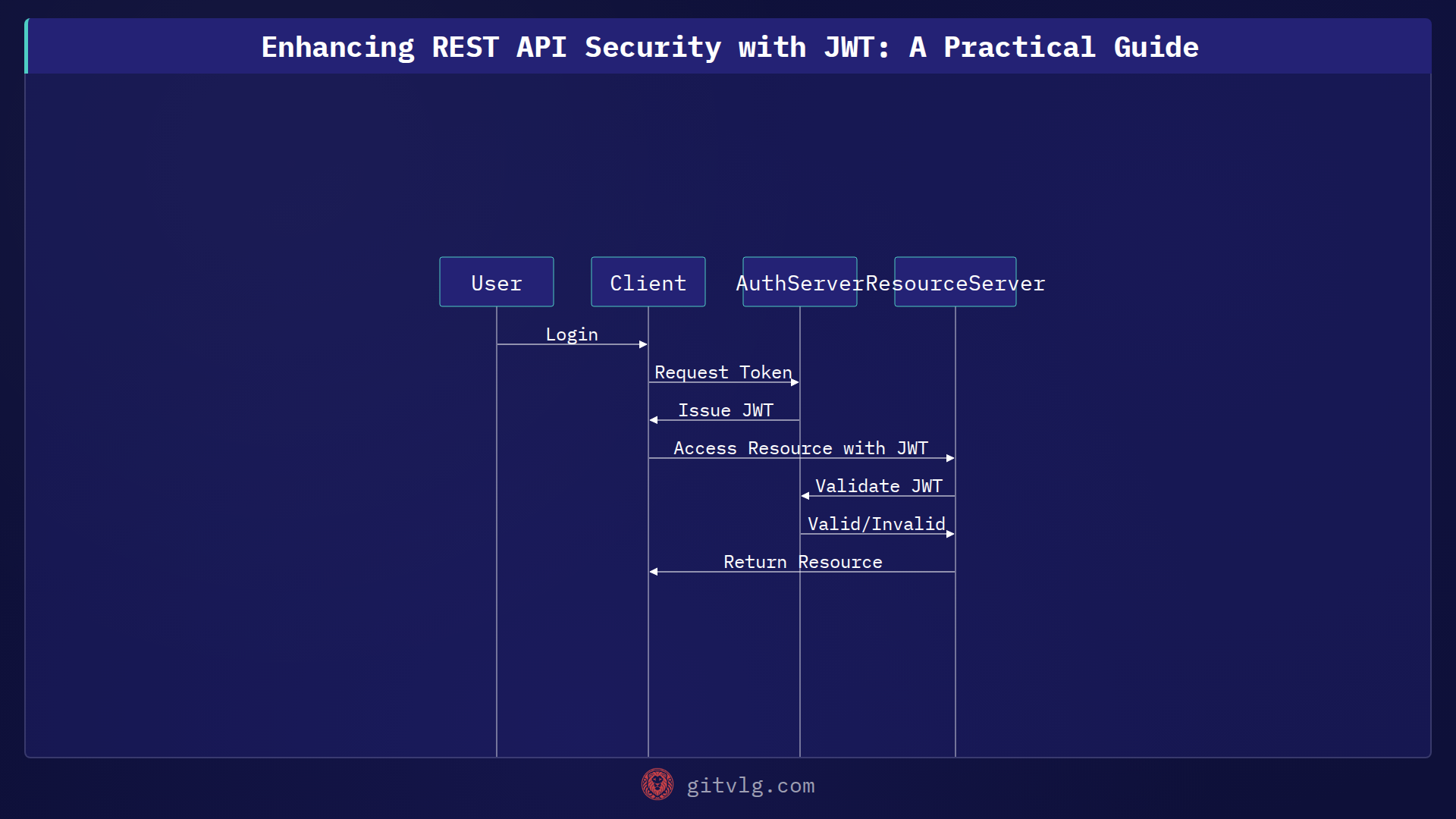
In modern web development, securing REST APIs is paramount. JSON Web Tokens (JWT) offer a robust and flexible mechanism for authentication and authorization. This post explores how we're leveraging JWT to enhance the security of the qa-portfolio-pro project's APIs, focusing on a practical approach to token generation, validation, and usage.
JWT Implementation
Token Generation
The first step is generating a JWT when a user successfully authenticates. This process typically involves the following steps:
- User Authentication: Verify the user's credentials (e.g., username and password) against a database.
- Payload Creation: Construct a payload containing user-specific data, such as user ID and roles. Avoid including sensitive information in the payload.
- Signing: Sign the payload using a secret key and a chosen algorithm (e.g., HMAC256). This signature ensures the token's integrity.
Here's a generic example of JWT generation in a hypothetical application:
// Example: JWT generation (replace with your actual implementation)
$payload = [
'user_id' => 123,
'username' => 'example_user',
'role' => 'administrator',
'exp' => time() + (60 * 60) // Token expiration time (1 hour)
];
$secretKey = 'your-secret-key'; // Replace with a strong, randomly generated key
$algorithm = 'HS256';
$jwt = JWT::encode($payload, $secretKey, $algorithm);
// Return the JWT to the client
echo $jwt;
Token Validation
Once the client receives the JWT, it includes it in the Authorization header of subsequent requests. The API then needs to validate the token before processing the request.
- Token Extraction: Extract the JWT from the
Authorizationheader (e.g.,Bearer <token>). - Signature Verification: Verify the token's signature using the same secret key used for signing.
- Expiration Check: Ensure the token has not expired.
- Payload Validation: Optionally, validate specific claims within the payload (e.g., user roles).
// Example: JWT validation (replace with your actual implementation)
$token = $_SERVER['HTTP_AUTHORIZATION']; // get token from header
$token = str_replace('Bearer ', '', $token);
try {
$decoded = JWT::decode($token, new Key($secretKey, $algorithm));
// Token is valid
$userId = $decoded->user_id;
$userRole = $decoded->role;
// Proceed with processing the request
} catch (Exception $e) {
// Token is invalid or expired
http_response_code(401); // Unauthorized
echo 'Invalid token';
}
Using JWT for Secure Endpoints
With JWT implemented, protect specific API endpoints by requiring a valid token. This ensures that only authenticated and authorized users can access sensitive data or perform certain actions. For instance, a route could only be accessible to users with the 'administrator' role, extracted from the token's payload.
Benefits Observed
Enhanced Security
JWT provides a stateless authentication mechanism, reducing the server's overhead. The signed token ensures that the data hasn't been tampered with during transmission, enhancing API security.
Improved Scalability
Since JWT is self-contained, the authentication process does not rely on server-side sessions. This makes the API more scalable, especially in distributed environments.
Fine-Grained Access Control
JWT's payload can contain detailed information about the user's roles and permissions, enabling fine-grained access control to different resources. Only authorized users can access sensitive data or perform specific actions.
Conclusion
Implementing JWT authentication has significantly improved the security and scalability of the qa-portfolio-pro project's REST APIs. By focusing on secure token generation, robust validation, and fine-grained access control, we've created a more resilient and trustworthy system. As a next step, explore integrating refresh tokens to improve user experience by allowing longer session times without compromising security.
Generated with Gitvlg.com